Documentation Index
Fetch the complete documentation index at: https://docs.levelblue.com/llms.txt
Use this file to discover all available pages before exploring further.
| Role Availability | Read-Only | Investigator | Analyst | Manager |
|---|
What Is Correlation?
Correlation is a process performed by the correlation engine in USM Anywhere. It identifies potential security threats by detecting behavior patterns across different types of , which produce disparate yet related events. Correlation links different events, turning data into more useful information. The logs received and processed by USM Anywhere carry important information such as what your users are doing, what data is being accessed, how your system and network are performing, and if there are any security threats or attacks taking place. However, reading logs has these disadvantages:- Logs vary from system to system or even from version to version on the same system.
- Logs have limited perspective because each system sees events from its own perspective.
- Logs are static, fixed points in time without the full context or sequence of related events.
- Make informed decisions on how to respond to security threats
- Validate the effectiveness of existing security controls
- Measure and report compliance
- Detect policy violations
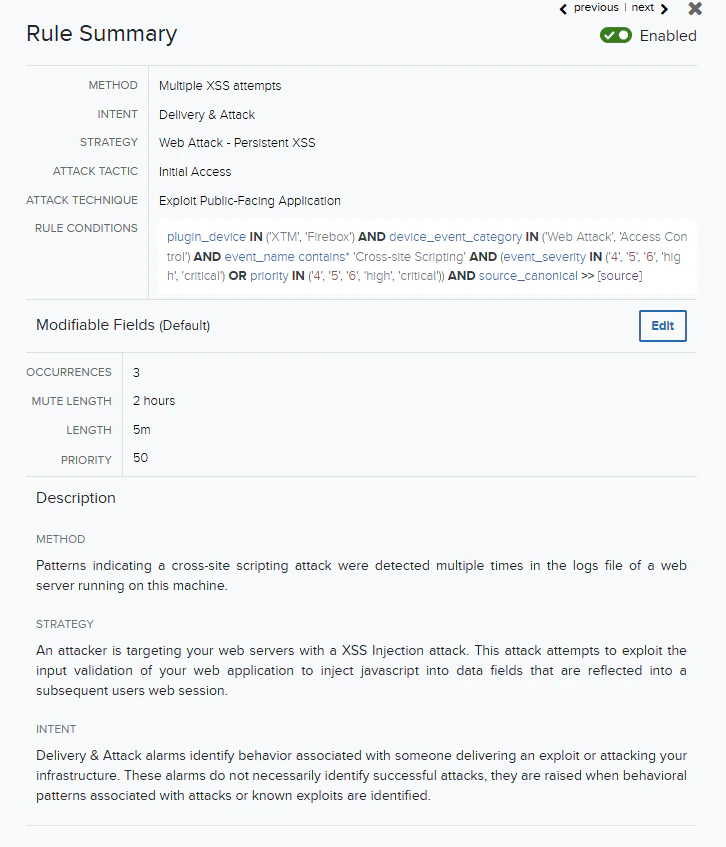
Correlation Rules Structure
This is the structure of correlation rules: Intent — Strategy — Method. The structure uses a three-tiered model for describing an observed behavior:- Intent: The first tier is the “intent” of the behavior. This roughly maps to the “intrusion kill chain” to provide an understanding of the context of the behavior.
- Strategy: The second tier is the strategy the took, used to describe the methodology employed.
- Method: The third tier is the “method” of the behavior, used to describe the details of the particular methodology.
| Intent | Description |
|---|---|
| Behavior indicating a compromised system. | |
| Exploitation & Installation | Behavior indicating a successful of a , backdoor, or remote access trojan being installed on the system. |
| Delivery & Attack | Behavior indicating an attempted delivery of an exploit. This can include detection of malicious email attachments, network-based detection of known attack payloads, or analysis-based detection of known attack strategies such as an SQL injection. |
| Reconnaissance & Probing | Behavior indicating an actor attempting to discover information about your organization. This is broad-based, including everything from to to open-source intelligence. |
| Environmental Awareness | Behavior and status about the environment being monitored. This includes information about services running, behavior of users in the environment, and the configuration of the systems. |
USM Anywhere Correlation Rules
USM Anywhere provides built-in rules and adds more every week through the LevelBlue Labs™ . Some of these rules are generic, which means that the rule can match data from different data sources. For example, the following rule matches data from all web datasources: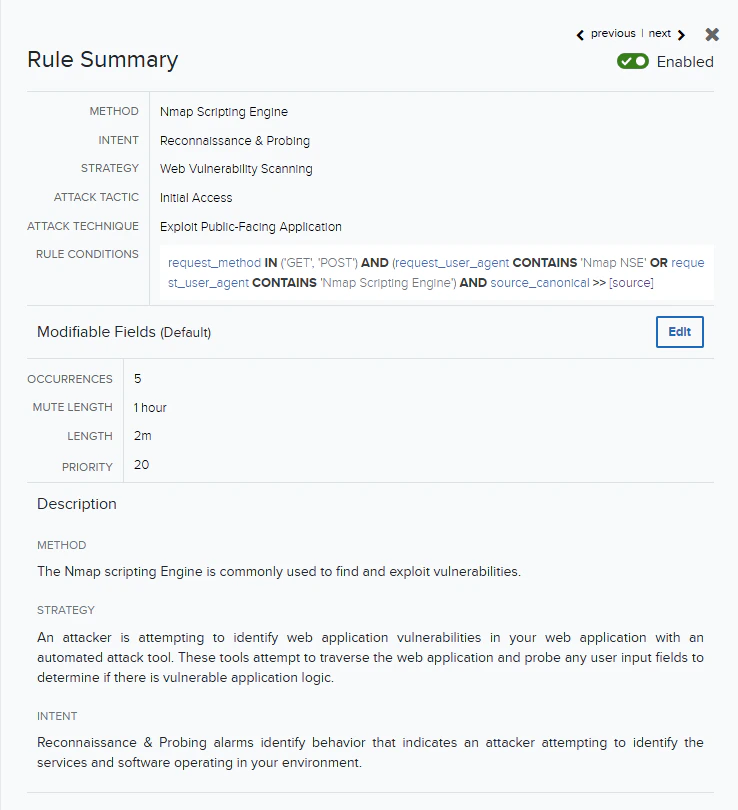
Note: When a more specific rule exists in USM Anywhere, it takes precedence over the generic rule.