Role Availability | ❌ Read-Only ❌ Investigator ✔️ Analyst ✔️ Manager Use the BlueApp for Palo Alto Networks PAN-OS to access the Palo Alto Networks response , which enable you to quickly respond to threats identified by USM Anywhere. You can create response action rules in USM Anywhere that automatically trigger when or match the criteria that you specify. For example, you might create a rule where USM Anywhere automatically sends the host information for malware infections that it identifies to the connected Palo Alto Networks device as a request to tag the host for policy enforcement.Documentation Index
Fetch the complete documentation index at: https://docs.levelblue.com/llms.txt
Use this file to discover all available pages before exploring further.
All Group and Tag names will default to lowercase in USM Anywhere to avoid any potential confusion over letter casing.
-
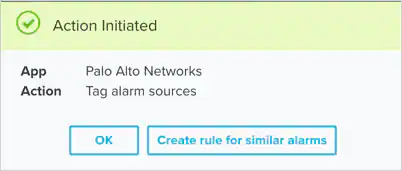
From an Applied Response Action: You can automatically create a rule using the response action that you apply to an existing alarm or event. This makes it easy to set the matching conditions for the rule based on the existing item and use the same settings that you applied to that item.
In the confirmation dialog box, click Create rule for similar alarms or Create rule for similar events.
-
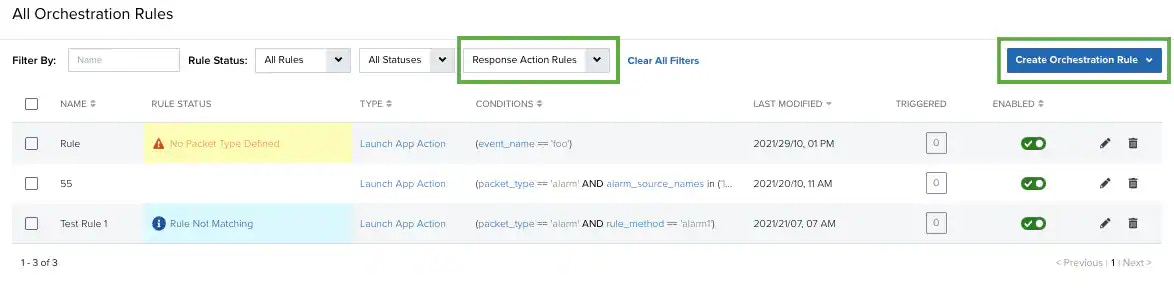
From the Rules page: The Rules page provides access to all of your orchestration rules. The Orchestration Rules list includes suppression rules, alarm rules, event rules, filtering rules, notification rules, and response action rules. You can create new rules using the specific matching conditions that you define, as well as edit, delete, and enable or disable rules. See Orchestration Rules for more information about managing orchestration rules.
In the left navigation menu, go to Settings > Rules > Orchestration Rules. Then click Create Orchestration Rule > Response Action Rule to define the new rule.
- Enter a name for the rule.
- For the Action, select the action you want to launch. You can launch an action to tag the destination host or source for an alarm or an event.
-
Enter the Palo Alto Networks Tag Name that you want to apply to the host.
-
At the bottom of the dialog box, set the rule condition parameters to specify the criteria for a matching alarm or event to trigger the rule.
- This section provides suggested property/value pairs from the selected alarm or event that you can use as conditions for the rule. Click the
 icon to delete the items that you do not want to include in the matching conditions. You can also add other conditions that are not suggested.
icon to delete the items that you do not want to include in the matching conditions. You can also add other conditions that are not suggested. - If you create the rule from the Rules page, you must use the Add Condition and Add Group functions to define the property/value pairs that you want to use as conditions for the rule.
- At the bottom of the dialog box, click More to display the optional multiple occurrence and window-length parameters.
Conditional Expression
Select an operator and add one or more conditions to form the conditional expression. You can include a condition group to evaluate a subset of conditions. The Current Rule pane displays the constructed expression in standard syntax. The box displays a red border if the expression is syntactically invalid as currently specified. A valid expression is required to save the rule definition.Select the operator used to determine the match for multiple conditions:- AND: Match all conditions.
- OR: Match any one condition.
- AND NOT: Exclude items matching all conditions after the first.
- OR NOT: Include all items that do not match any conditions after the first.
Occurrences
Specify the number of event or alarm occurrences that produce a match on the conditional expression to trigger the rule. The default value is 1. You can enter the number of occurrences or use the arrow to scroll the value up or down.USM Anywhere uses this in conjunction with the Length option to specify the number of occurrences within a time period that will trigger the rule. For example, you can define a rule to trigger for an unauthorized access attempt when a failed SSH login occurs three times within a five-minute window.Length
Specify the length of the window to identify a match for multiple occurrences. Enter the number and choose a time unit value of seconds, minutes, or hours. This time period identifies the amount of time that transpires from the first occurrence to the last occurrence. If the number of occurrences is not met within this period, the rule does not trigger. - This section provides suggested property/value pairs from the selected alarm or event that you can use as conditions for the rule. Click the
- Click Save Rule.
